IMDb has added AI-generated summaries from the text of user reviews. I noticed because I read this piece of garbage.
> Reviewers say 'Scarface' receives mixed reactions, with many praising Al Pacino's portrayal of Tony Montana, a Cuban immigrant navigating Miami's drug underworld. The film's style, violence, and Pacino's intense performance are commended.
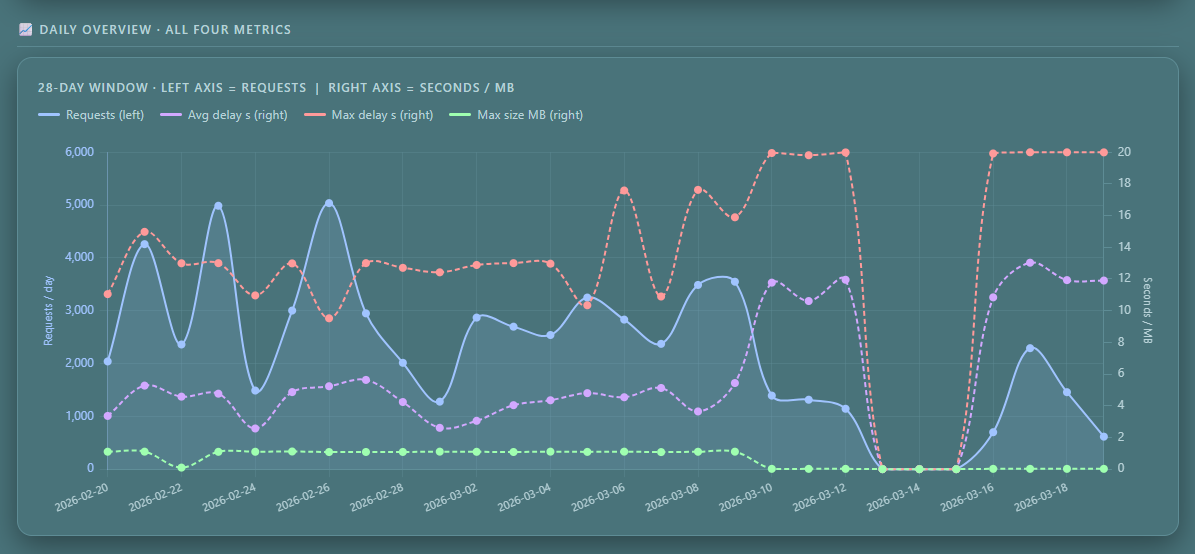
New reporting for The MIRE/C³, 28-day trends showing volumes, delays and sizes.
Since The MIRE/C³ is running in Neutral404 mode, size is almost zero. That will change at the end of the month.
And yes, The MIRE/C³ was off for 3 days #duetohumanerror
Work stuff - #OpenScience #FAIRdata #FoodSci #Foodindustry #FoodTech #fediverse - Discussion on tools etc.
So, I recently applied and was accepted to a COST action (CA24145 link https://www.cost.eu/actions/CA24145/ ). The goal is to standardize methodologies for technofunctional properties of food - so does it foam, how does it foam etc, solubility, emulsion, etc.. This is riveting stuff for food engineers and scientists, I tell you. And if we have shared methods, we could also share results and replicate stuff.
My question to whom it might interest is how would you set up communication to the group? Do you have an example? I'm pretty sure there should be better ways of keeping tabs on peoples discussions and versions of common files than a shared folder somewhere and emails with a lot of cc:s updated manually.
One example that comes to my mind would be ImageJ and it's respective forum at Image.sc - I think that is a nice way of doing it, but I'm sure there are others.
I'm also having a gut feeling or wish that federation as in the fediverse might help - the end goal is not get just one (choke) point on the topic but facilitate collective building, between unis, rtos, companies, researchers, industry, smes etc.
So, looking forward to hearing from you - please share and boost for reach!
The Stryker data wiping attack via Intune and the attempted attack on the Polish National Centre for Nuclear Research (NCBJ) show that geopolitical affairs also play a big role in cyber security.
In the Stryker data wiping attack via Intune that wiped “over 200,000 systems, servers, and mobile devices,” there are anonymous reports and rumours that employees’ own mobile devices, enrolled under a BYOD (Bring Your Own Device) initiative, were affected. Under that initiative an employee’s personal mobile device, such as a tablet or smartphone, can be enrolled via an Intune MDM profile, policies were supposedly applied and the devices were fully wiped to factory state, so personal data, apps, and pictures were unfortunately lost.
In a properly configured environment, an administrator would configure BYOD (Bring Your Own Device) via Intune to use a segmented work partition, otherwise known as a Work Profile. This solution creates a separate, segmented space that is secure for work‑related data and apps while keeping users’ personal data separate and inaccessible to the Work Profile. In the case of a remote wipe by either the company administrator or a malicious actor, only the Work Profile and its space would be wiped while users’ personal data would remain intact.
To further secure your Intune environment against wiper attacks like the one that affected Stryker, there are two controls you can implement:
The first control I would recommend is to require the use of either PassKeys or YubiKeys for all highly privileged accounts that each employee uses to perform sensitive and critical tasks. Combine this with a policy that such accounts cannot be used unless a PassKey or YubiKey is enrolled. This ensures that sensitive accounts are compliant and helps prevent MFA phishing, since an attacker would need physical access to the smartphone or the YubiKey device.
While both PassKeys and YubiKeys accomplish the same goals, there are minor differences between them:
PassKeys do not require dedicated hardware and can be used entirely via the Microsoft Authenticator app. PassKeys also allow syncing authentication method between devices, so when one device is lost you can still authenticate via another device. When an employee logs into a sensitive system, they are asked to authenticate via face recognition, fingerprint, or PIN and to scan a QR code to approve the login request using Bluetooth and an internet connection.
YubiKey require the dedicated hardware and the company to purchase a physical key. The private keys used for authentication are stored on the device itself in a dedicated, hardened chip that cannot be read by the user or a malicious actor. Because of how the private keys are stored and hardened, you cannot sync or backup them, however, if a privileged user loses their key or it breaks, an administrator can reset the affected account’s authentication method to enrol a newly issued key. While this method comes at a cost and some inconvenience, it offers a higher level of security than other methods. When an employee logs into a sensitive system, they need to insert the YubiKey into a USB port, enter the YubiKey PIN, and physically touch the YubiKey to complete authentication.
The second control would be to require approval from another employee when a wipe command is issued. This would stop an attack in its tracks if a highly privileged account is compromised and an attacker attempts to wipe devices in the environment. However, if PassKeys or YubiKeys are used for account authentication, the likelihood of a privileged account compromise is very low. To further lock down your environment, you can put the same type of control in place for other similarly sensitive actions or commands.
#Stryker #Intune #MDM #BYOD #Policy #Prevention #CyberPrevention #Cyber #CyberSecurity #CyberAttack
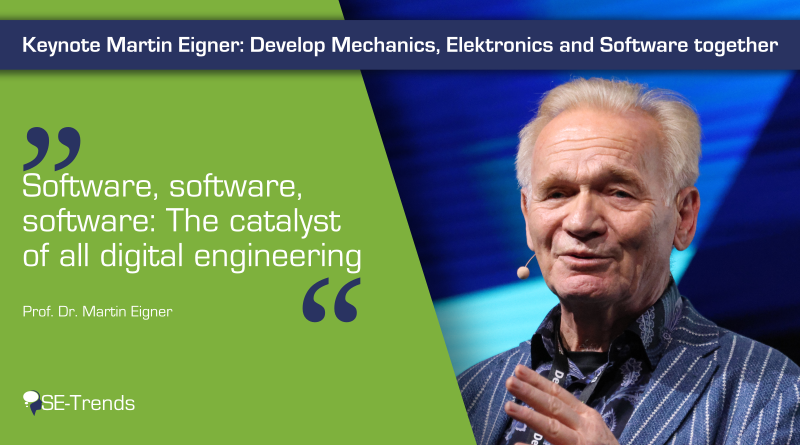
Keynote Martin Eigner: Mechanik, Elektronik und Software gemeinsam entwickeln
In dieser Keynote zeigt Martin Eigner, wie Software, Systeme und Services die Produktentwicklung verändern.
https://www.se-trends.de/keynote-martin-eigner/
#Automotive #Deutschland #Menschen #ProductVelocity #Veranstaltungen #ADAS #ALM #Integration #Komplexitt #MartinEigner #Modellierung #PLM #Services #Software #Versionierung
The #Windows 10 PC of my wife died, the good thing is that I've used the chance to set her up on Linux on a spare device. I've chosen zorin.com as it looks mostly like Windows and has a Debian/Ubuntu underneath.
Over the years I've convinced her bit by bit to use #Opensource apps, so I just installed the Linux equivalent.
The evil plan is to get her comfortable with that, then I don't have to think about upgrading to Win 11 or ever supporting it.
2026 the year of the Linux Desktop (in my home)
While doing some OSINT research, I realized how fragmented the workflow can be.
I often had to jump between multiple tools just to collect small pieces of information — one tool for usernames, another for domains, another for metadata, and sometimes manual searching in between. It quickly became messy and inefficient.
So I started experimenting with a small project to simplify that process.
GhostIntel is an OSINT-focused tool designed to help gather and organize publicly available information in a more streamlined way. The goal is not to replace existing tools, but to reduce the friction of switching between them.
Still experimenting and improving it.
If you're interested in checking it out or sharing feedback:
https://github.com/ruyynn/GhostIntel
Always open to suggestions from the infosec community.
While doing some OSINT research, I realized how fragmented the workflow can be.
I often had to jump between multiple tools just to collect small pieces of information — one tool for usernames, another for domains, another for metadata, and sometimes manual searching in between. It quickly became messy and inefficient.
So I started experimenting with a small project to simplify that process.
GhostIntel is an OSINT-focused tool designed to help gather and organize publicly available information in a more streamlined way. The goal is not to replace existing tools, but to reduce the friction of switching between them.
Still experimenting and improving it.
If you're interested in checking it out or sharing feedback:
https://github.com/ruyynn/GhostIntel
Always open to suggestions from the infosec community.
🚨 OpenProject CRITICAL XSS (CVE-2026-32703): Attackers with repo push access can inject persistent scripts via filenames, impacting all users viewing affected pages. Patch to 16.6.9/17.0.6/17.1.3/17.2.1+ now! https://radar.offseq.com/threat/cve-2026-32703-cwe-79-improper-neutralization-of-i-f2afc489 #OffSeq #XSS #OpenProject #infosec
H y o U m a n
R j o b
B e
N
E a
W i t h i n
A b o v e w h o r a t
T h i n g
N y
A
L
0
L
M
A t
T e r
H y 0 u m a n
(Y) O u r job be neat h, wi th in, (and) above
E l s e a l l (a) n
(W h)
(H)
Y
0
U
Man
N o m a t t e r
T a (c h e) k i n g a c c o u n t r e s p o n s (e) i
R e s p e c t r s o n a l s e l f
(A) b i (w arm th)
L i (gh) t
A s
G
K
I n
(Wh) y
#poem #poetry #individuality #authenticity #sovereignty #tolerance #reconciliation #letterlab #source #zero #writing #letterportals #wordpuzzles #programming #perception #encryption #code #polarity #one #unity #binity #trinity #quadrinity #singularity #duality #ternity #quaternity #p01 #fediverse #exquisitesocial
[I'm reposting something I posted earlier, having now blocked a troll who didn't contribute anything useful.]
Whew. I have finally gotten around to reading this essay by Dario Amodei, the CEO and co-founder of AI company Anthropic, which has developed the LLM Claude.
I think everyone should read this, whatever your thoughts are about AI. Even reading just the first part would be worthwhile, though I recommend all of it.
https://www.darioamodei.com/essay/the-adolescence-of-technology
2026 marks a monumental shift in marketing beyond 'digital.' AI will upend commercial models, reshape brand expectations from partners and demand new measures of efficient growth. CMOs face the herculean task of rewiring the marketing function. https://www.forrester.com/blogs/forresters-complete-view-powers-marketing-excellence-why-cmos-agencies-and-martech-leaders-need-integrated-insights/ #Marketing #Strategy #AI #Forrester
🔎 CVE-2026-32731 (CRITICAL, CVSS 10): Path traversal in ApostropheCMS import-export <3.5.3 lets attackers write files as Node.js user via crafted archives. Upgrade to 3.5.3+ and restrict permissions now! Details: https://radar.offseq.com/threat/cve-2026-32731-cwe-22-improper-limitation-of-a-pat-efa014e1 #OffSeq #CVE202632731 #infosec #cms
As warfare becomes increasingly high-tech, Ukrainian towns are fighting back in a surprisingly low-tech way: covering their cities in corridors of netting. While effective, the nets leave residents on edge. “Now we see all these nets here, and we all understand that it’s a sign of something. That the drones can reach any part of the city.” Read more from @npr
We’ve seen questions around PH4NTXM regarding source code, audits, and overall transparency.
To clarify:
PH4NTXM is a commercial, closed system.
At this time, it is not open-source and does not provide public access to internal components.
This model is intentional and allows us to maintain a controlled, consistent operating environment.
For those interested in exploring the project in a more accessible way, we offer PH4NTXM-LITE, which reflects the direction and core philosophy of the system.
We understand that different users have different requirements.
If full transparency and community-driven development are priorities, there are excellent solutions built around that model.
PH4NTXM follows a different approach—focused on controlled deployment, consistency, and defined operational boundaries.
This direction may evolve over time, but this is the current model.
Choose what best fits your needs.
#ph4ntxm #linux #debian #os #live #privacy #security #opsec #infosec #research #tech
As warfare becomes increasingly high-tech, Ukrainian towns are fighting back in a surprisingly low-tech way: covering their cities in corridors of netting. While effective, the nets leave residents on edge. “Now we see all these nets here, and we all understand that it’s a sign of something. That the drones can reach any part of the city.” Read more from @npr
Whoa, Junie! I said I wanted to plan out some incremental changes, not for you to go off and do everything on your own without asking me for input. WTF?!
This is why tech writing is important! Really strong guide for blind people! This was so refreshing to see, I read this twice! Tech writing is important! How to Perform a System Update and Enable Text to Speech During Nintendo Switch 2 First-Time Setup | Nintendo Support https://en-americas-support.nintendo.com/app/answers/detail/a_id/68477/~/how-to-perform-a-system-update-and-enable-text-to-speech-during-nintendo https://en-americas-support.nintendo.com/app/answers/detail/a_id/68477/session/L2F2LzEvdGltZS8xNzczNzM0MDQ1L2dlbi8xNzczNzM0MDQ1L3NpZC9mVUpLWHM3VlVyS1Q0QkpIVXZOMm9hSndZV05LNWslN0VmakVIcUx3MjFQYkV1bE5pUnQzVE9rTFc3a0t1QkI2azZFUWIyTTZibW9qd2UlN0VITm01NUo3UmlfNFlXVjF6QjFZYzBLblNVTkhZeklNRWptenNBUjlwcTR3JTIxJTIx #Tech #Writing #Documentation
Whew. I have finally gotten around to reading this essay by Dario Amodei, the CEO and co-founder of AI company Anthropic, which has developed the LLM Claude.
I think everyone should read this, whatever your thoughts are about AI. Even reading just the first part would be worthwhile, though I recommend all of it.
https://www.darioamodei.com/essay/the-adolescence-of-technology
Middle managers are the missing link in AI adoption, according to MarTech research. While leadership and teams are on board, AI initiatives stall because middle managers are overlooked. They bridge strategy and execution but lack support. Organizations that empower them see higher AI project success. https://martech.org/middle-managers-are-the-missing-link-in-ai-adoption/ #Marketing #Strategy #AI